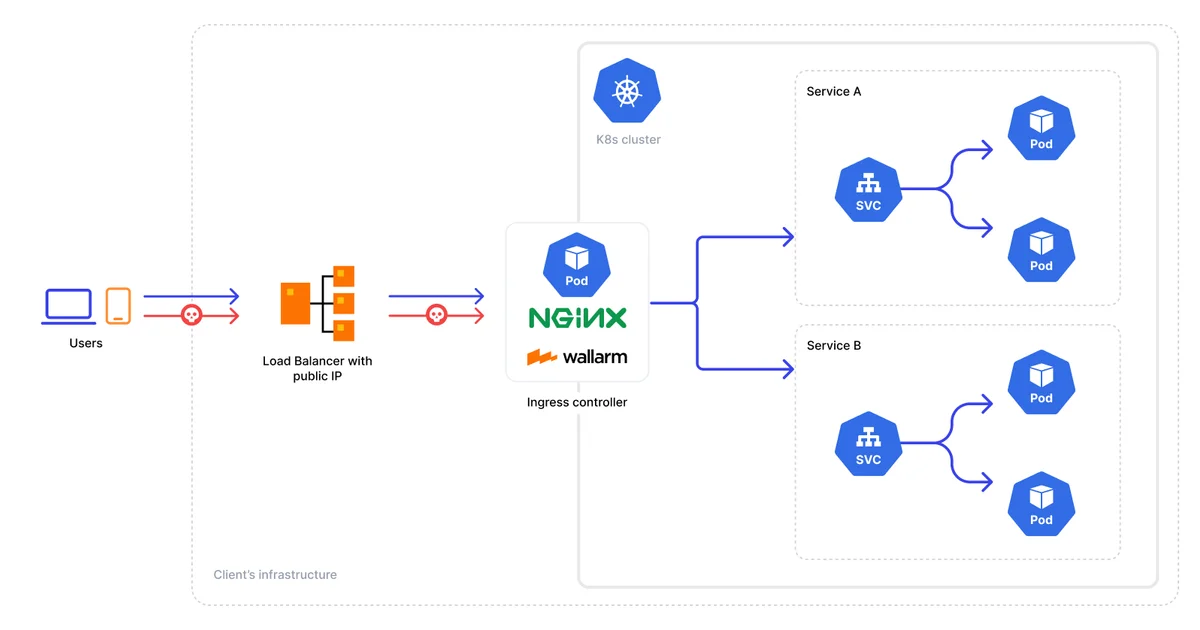
Kubernetes Ingress Controllers: Routing External Traffic the Right Way
Compare Kubernetes Ingress controllers -- nginx-ingress, Traefik, HAProxy, Contour. Learn path and host routing, automatic TLS with cert-manager, and the Gateway API.
Compare Kubernetes Ingress controllers -- nginx-ingress, Traefik, HAProxy, Contour. Learn path and host routing, automatic TLS with cert-manager, and the Gateway API.
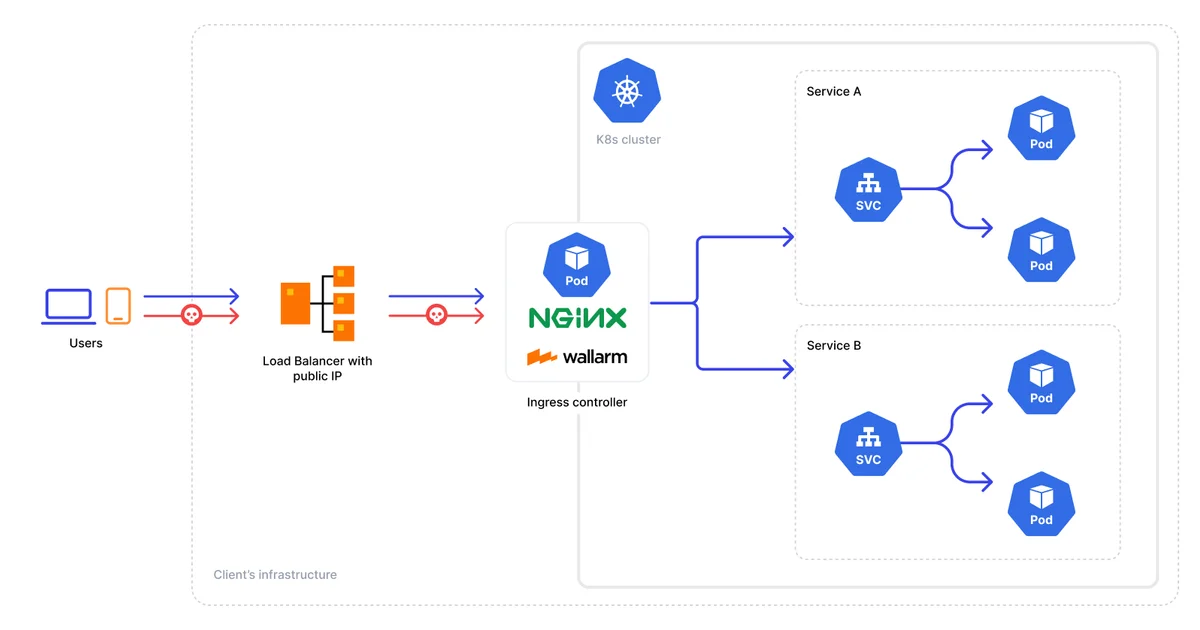
Harden Docker containers with minimal base images, non-root users, dropped capabilities, read-only filesystems, CVE scanning in CI, and Kubernetes Pod Security Standards.
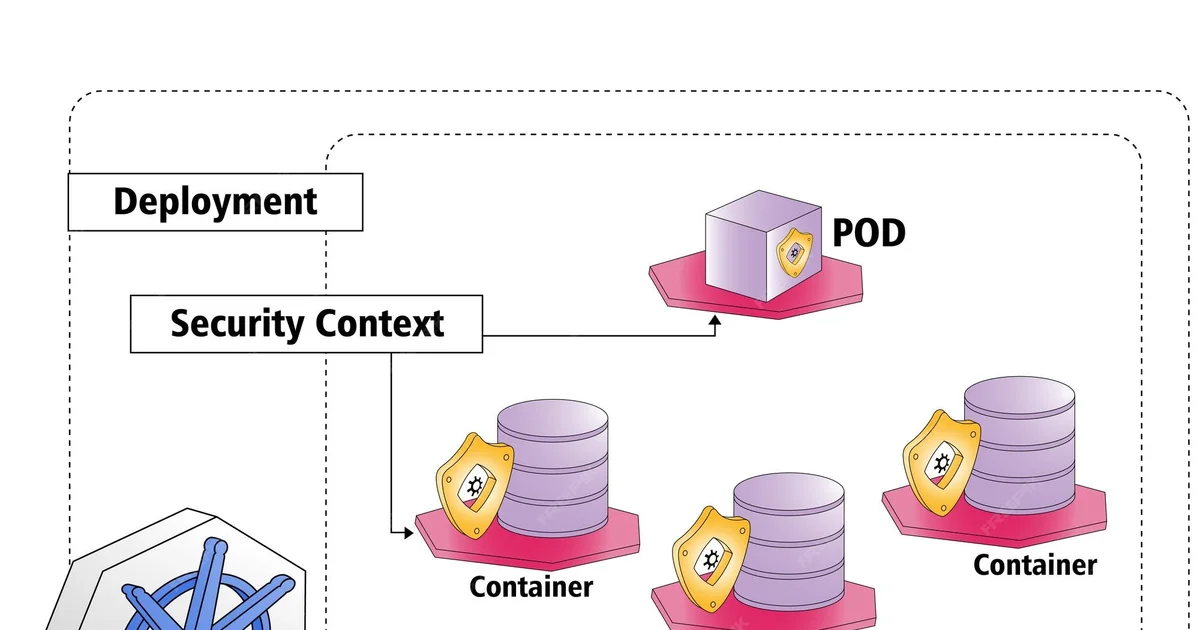
Build in one stage, copy to a minimal runtime image. Practical multi-stage Dockerfile examples for Go, Node.js, and Python that cut image sizes by 10x or more.
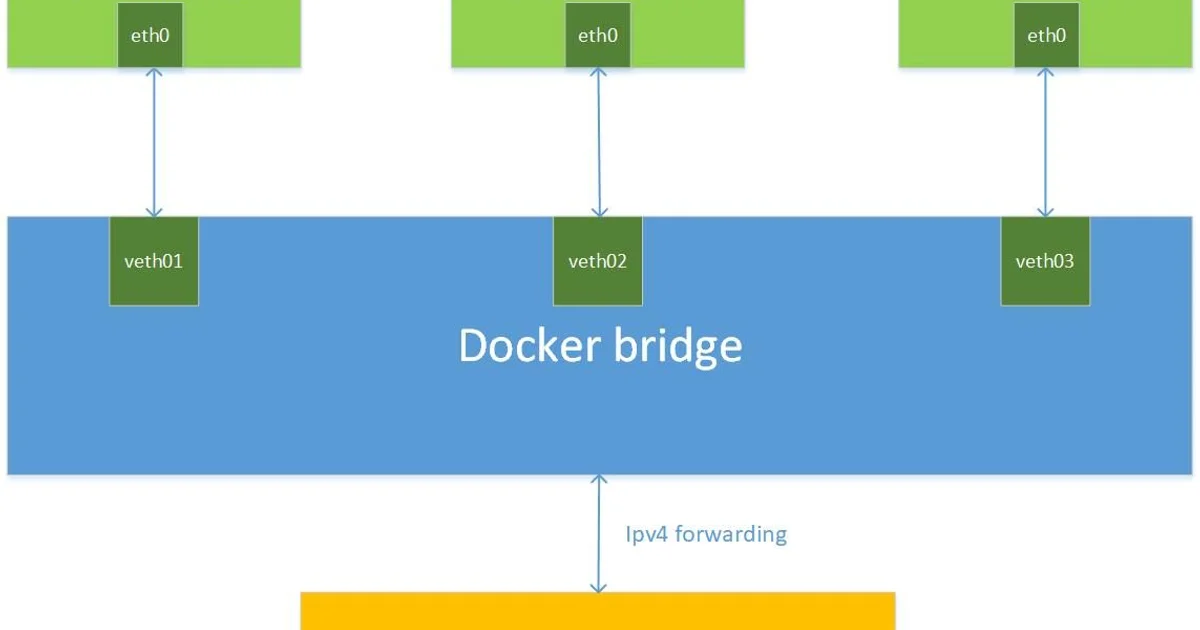
Understand Docker's four network drivers -- bridge, host, overlay, and none. Learn how container DNS resolution works, when to use each driver, and how port mapping actually functions.

Language models process tokens, not words. Learn how BPE tokenization works, what the context window really is, and how the KV cache speeds up generation — with real pricing comparisons across OpenAI, Anthropic, and Google.
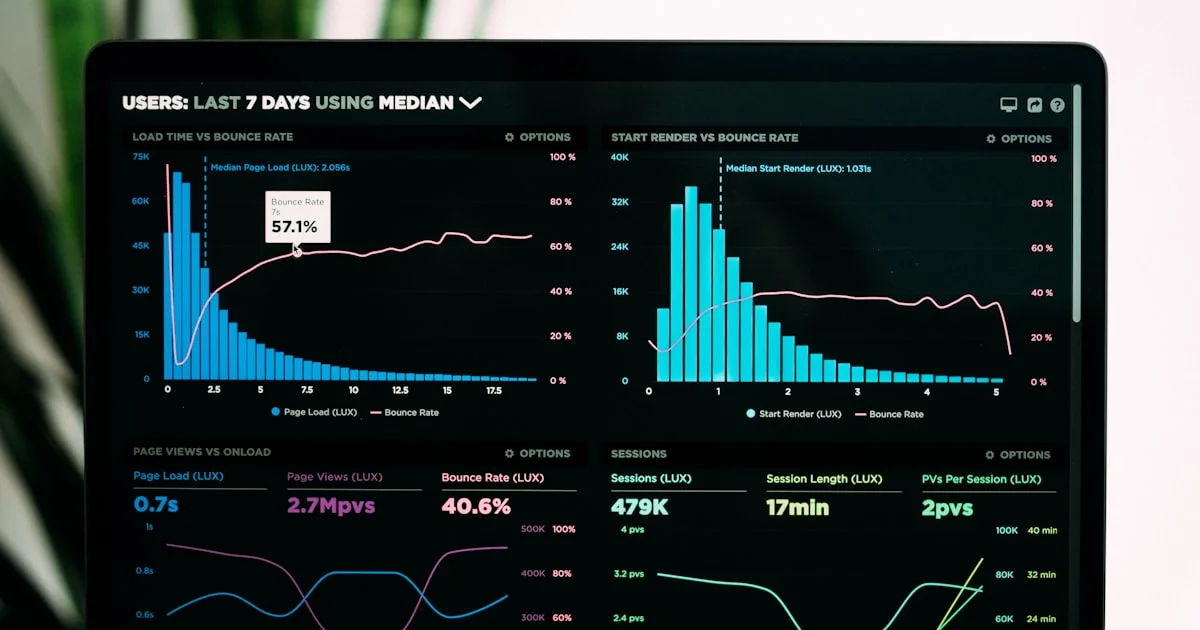
Observability rests on three pillars: logs, metrics, and traces. Learn what each pillar does, how to instrument them, the RED and USE frameworks, and how to choose an observability platform without blowing your budget.
Event-driven architecture decouples services through message brokers like Kafka, RabbitMQ, and SNS/SQS. Learn when EDA is the right choice, how to implement it, and the patterns that make it work in production.
An honest comparison of JWT and session token authentication. Covers JWT structure, signing algorithms (RS256 vs HS256), common vulnerabilities, the revocation problem, and when each approach is the right choice for your architecture.

A complete guide to PostgreSQL index types. Learn when to use B-Tree, Hash, GIN, GiST, BRIN, and partial indexes with real SQL examples, EXPLAIN ANALYZE verification, and index maintenance strategies.
New articles delivered to your inbox. No spam.